Setting up Accops HySecure in Azure and AWS Clouds
When we started working in hybrid mode, VDI (Virtual Desktop Infrastructure) became very popular. It is nothing but a company-provided virtual desktop that you can access from anywhere. It is as secure as working from the office. You login into it, do your work, and log off. All your data will store in a centralized location.
In this space, big players are Citrix VDI and Vmware Horizon. Their setup takes time to build up. On a similar line, you will see Azure Virtual Desktop (AVD) and Amazon Workspace in public cloud space. Accops is one of the VDI solutions which you can set up in an on-premise environment and even in the cloud as well.
Accops Stands for Access Operations. They started the journey in the year 2012 with HQ in Pune, India. Till now they have served over 700+ Enterprise customers serving 250 skilled people. They have 150+ channel partners.
They have a wide product range but we are going to talk about two major products. In this article, we will discuss HySecure product. I will dedicate the next article to discovering HyWorks – Desktop and App Virtualization
HySecure is a VPN gateway solution, that provides Zero Trust Network Access (ZTNA) for a VDI environment. Users can connect to VDI by HySecure web access or by the HySecure desktop client tool. It provides options to log in with the Organization Active directory and MFA can be enforced as additional security. Restrict users by in-built policies. With HySecure, you can do host scanning, device context security, Endpoint, and internet control. You can connect to your office PC, internal or any external applications by publishing it.
Along with VPN capability, you can do session and policy management, application proxy, and audit logging. To perform this, HySecure provides a management console. It comes with its inbuilt MySQL – MariaDB database. Here is the architecture of HySecure.
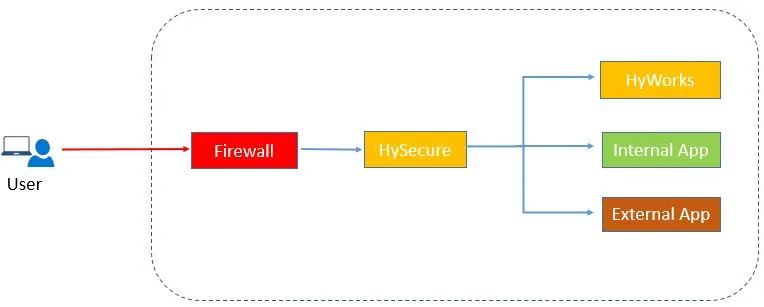
Today we will see how to install HySecure on the standalone instance in Public Clouds, like Azure and AWS. Installation and configuration steps are the same. It is recommended to deploy the server in the DMZ zone.
Pre-requisite:
- For 100 VDI users, you need 4 CPU and 8 GB RAM capacity SKU with 100 GB space
- Allow port Inbound – 443 and 22, Outbound – 443
- Azure Contributor/AWS Admin permission to create a resource
- Windows OS system to access HySecure remotely via the web or client tool
Installation Steps
- Login into the Azure portal, go to virtual machine serviceand click on create to start VM creation. Provide Subscription name, resource group, VM name. select region, availability group. select an image from the marketplace. Search for the HySecure image. select Azure Cloud Gateway’s latest image. select SKU size, and set user name and password. select disk and network. you can keep the remaining option default. Review and create it.
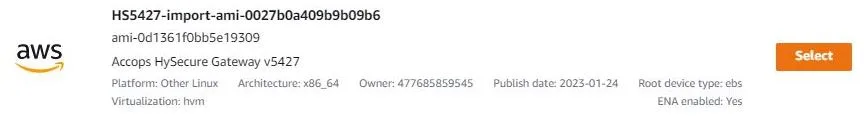
If you go with an AWS instance, select the EC2 instance. provide name. Select the Accops HySecure image from the marketplace. Generate Key pair. Select VPC, subnet, and network Security group. You can keep the remaining setting for default.
2. To access HySecure URL, you need one windows desktop system in the same network. You can access https://<HySecure IP>.
3. You will see a welcome screen with a message to configure HySecure now. Click on it. Accept EULA to proceed and submit.
4, Select HySecure Gateway on the virtual machine and submit.
5. Provide host configuration containing hostname, default gateway, and DNS server. Provide interface configuration containing IP address and subnet mask. Set date and time settings.
6. Default license is for 5 concurrent users in the trial version. You can extend it later with Accops Support. It will valid for 30 days. click on submit and continue. Go with a fresh installation.
7. As we access HySecure internally, select default Accops internal CA. You also get the option to use external CA as well if you have one. You need to provide demographic details to generate SSL certificate. The installation will create one account with a Security officer role with a passphrase. This passphrase is non-transferable.
8. Download the Accops HySecure Client from the HySecure login page on the windows system. Install it. Do reboot after installation. Open the Client tool, put the HySecure IP address, and check on login with a digital certificate. Click on the Action tab at the top, Enroll Client SSL Certificate. Put the passphrase, add and confirm the new password. Login with a new certificate and password.

Open the HySecure Management Console. Go to settings -> service config -> Gateway State -> click on Run State.
Configuration Steps :
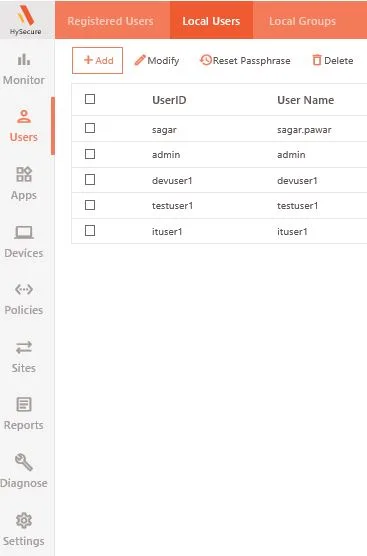
- On the HySecure Dashboard, you get the below options.
- Monitor – Monitoring the status of Users, devices, and licenses
- User – User and group creation
- App – Creating Application and Application Group
- Device – Device registration
- Policies – Governance of users and endpoint devices
- Sites – Cluster Setup
- Reports – Tracking logs and generating the reports of user, admin, and Apps
- Diagnostic – Troubleshooting connectivity
- Setting – HySecure Configuration
2. Check the Authentication domain. HySecure can integrate with external Active directory servers. If you do not have one, you can use the default one to create users as shown below. If you are using external AD, open the required ports for communication. For this demo, I have created a few local users as a low-security users and local groups like dev, test and IT. There are total 5 roles to be configured. Other than low-security users, other roles need a passphrase and certificate for login. Along with HySecure, you can use HyID product if you want to enable MFA.
3. Go to application section, and create one application for desktop access. Select RDP Type from the drop-down list, Provide the VM IP which you want to access and submit it. I am keeping the remaining options default for this demo.
4. Go to the application group section. click on create and provide the Application group name and select a newly created application. Submit it to apply changes. There is one option to define security level, by-default it is low, which means you can add only the Low-Security User role. If you check it, you can add users with high-level security user roles i.e. High Security User, Administrator, Security Officer and Monitoring User.
5. Go to policies, and create ACL (Access Control List) to provide access to users on the application group.
Select the Application Access type from the list. Provide a name to access the list. Select HySecure Domain, Authentication server, assignment and native Group from the drop-down list. The user group will auto-populate to select from. Select the required user group and Application group from the list. I keep the remaining field blank as I do not want to apply any time-based filter and access control validation on it.

6. In the trial period, you will get 5 concurrent licenses. To get a new license, Go to general setting -> License Management -> get a license and Send a mail Accops team to get the serial key. Either you can go with a Subscription license (Time Bound) or a perpetual license (lifetime validity)
Testing :
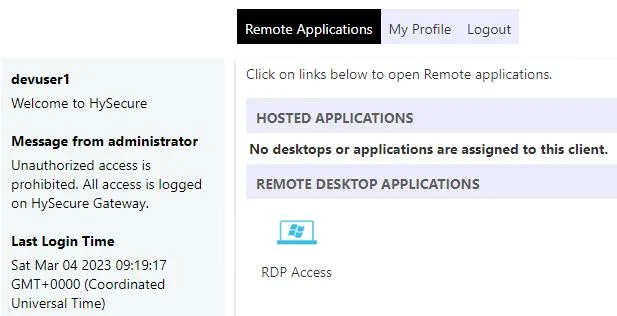
- Login into HySecure web UI with the user. You will see RDP access application group will be visible to you.
2. You can double-click on it and log in with credentials. If you enable SSO in RDP Access, login will be done automatically.
I hope you have enjoyed the article the way I enjoyed it while testing and writing it. Thanks for reading. Meet you in the next article related to Accops HyWorks.
Leave a Reply